09 - Cybersecurity and Incident Response
Class: CYBR-405
Notes:
Module Objectives
By the end of this module, you should be able to:
- Describe basic functions of a network
- Explain the process of defense in depth
- Describe indicators of compromise
- Describe incident response lifecycle
Network High

- Think of your highschool days
- Nobody talk to each other, it was hard to communicate but you could talk to yourself
- Then there was some problems with our comms, and we had to come up with TCP, this is the base of the internet, all comms go through this
- TCP guarantees communication
- UDP just forwards packets as fast as possible
Birth of TCP/IP
In the early 1970s, the U.S. Department of Defense funded a project through DARPA to solve this problem. Two researchers, Vint Cerf and Bob Kahn, were tasked with creating a protocol that could allow different networks to communicate with each other.
Transmission Control Protocol / Internet Protocol, or TCP/IP.
TCP/IP Continued
IP (Internet Protocol)
- Handles addressing and routing
- Moves packets from one computer to another across networks
- Does not guarantee delivery
IP figures out where the data should go,
and TCP makes sure it actually gets there correctly.
TCP (Transmission Control Protocol)
- Ensures reliable delivery
- Breaks data into packets
- Reassembles packets in order
- Retransmits lost packets
Early Internet

Defense in Depth
"An approach to cybersecurity in which a series of defensive mechanisms are layered in order to protect valuable data and information. If one mechanism fails, another steps up immediately to thwart an attack. This multi-layered approach with intentional redundancies increases the security of a system as a whole and addresses many different attack vectors".
- People
- Technology
- Operations
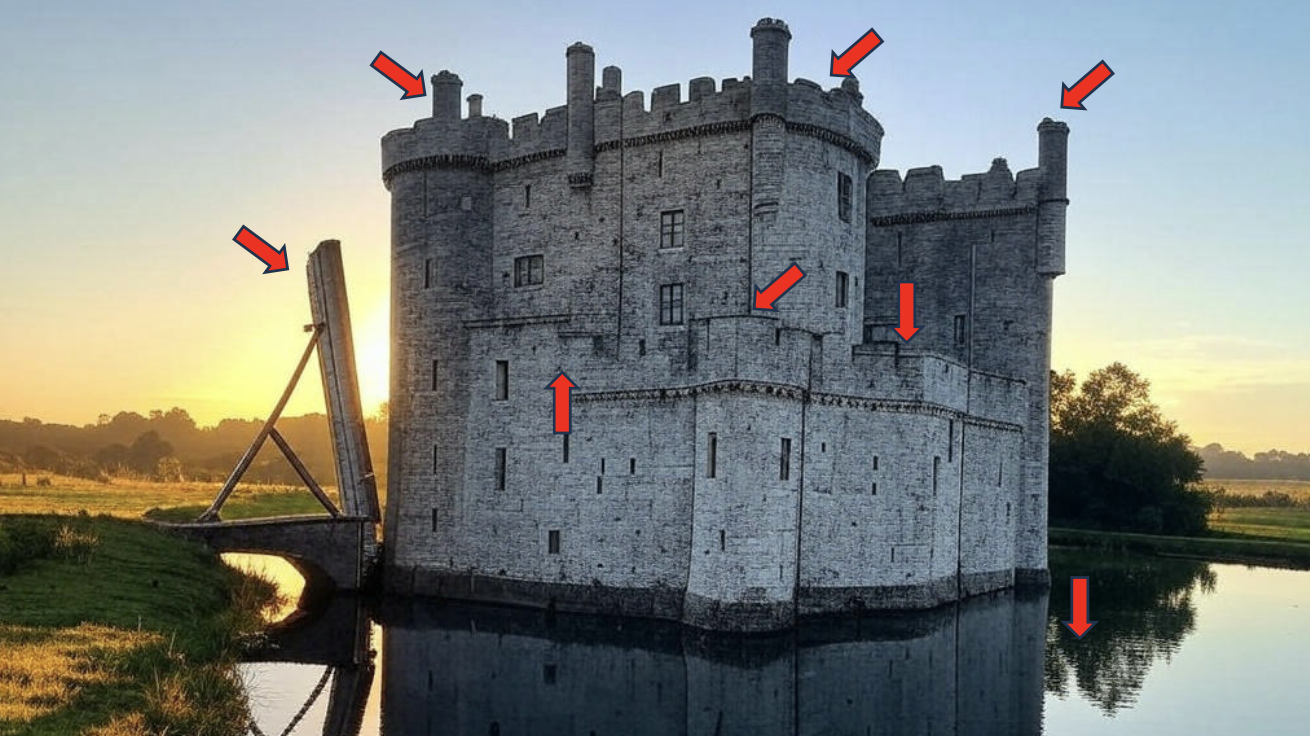
Notes:
- The first line of defense of a castle is the water
- Then we have wholes to defend the castle
- Then we have towers
- And so on
"Hackers don't break in, they log in"
1. Stolen Credentials
2. Exploited Vulnerabilities
Notes:
- Identity & Access Management (IAM): is basically who you are
- In the castle, you get the keys from a knight, you get in (you log in)
- You need to be able to detect a knight walking into the front room
- If you can pretend to be a knight, find the authentication of the king, we call this the pivot to get access (usually an employee)
Weakness
- The "castle approach" focuses defenses on external threats.
- Once inside, the only thing controlling movement is easily defeatable by changing roles (RBAC).
- An admin (role) can easily move laterally (spread) to other systems increasing the negative impact to the organization.
- The volume of different applications and frequency of different vulnerabilities (i.e. backdoors) makes it challenging to keep everything patched to stay ahead of our adversaries.
Notes:
- Tactics:
- Defense Evasion
- Lateral Movement
- Exfiltration
- There is different techniques within tactics
- Techniques describe way to mitigate the behavior

- They have a database of vulnerabilities for basically every single vulnerability in any product you can think of
- This is bad for attackers! becuase they will now have the same information
Indicators of Compromise
How do you know when you are sick?
Fever
Feel Bad
Coughing
Tired
Throwing up
Upset Stomach
Cold Sweats
Etc.
How do you know when you got attackerd?
- Unusual traffic going in and out of the network
- Unknown files, applications, and processes in the system
- Suspicious activity in administrator or privileged accounts
- Irregular activities such as traffic in countries an organization doesn't do business with
- Dubious log-ins, access, and other network activities that indicate probing or brute force attacks
- Anomalous spikes of requests and read volume in company files
- Network traffic that traverses in unusually used ports
- Tampered file, Domain Name Servers (DNS) and registry configurations as well as changes in system settings, including those in mobile devices
- Large amounts of compressed files and data unexplainably found in locations where they shouldn't be
Anatomy of Cyber Attack
Reconnaissance
The threat actor uses the internet, social media, or other tools to discover likely attack courses.
Weaponization
Code and other tactics, techniques, and procedures are found or developed to exploit the target's vulnerabilities.
Delivery
Weaponized code is transmitted to the target.
Exploitation & Installation
The attacker uses the tactics to dismantle internal controls in the target to avoid detection.
Command & Control
This may Include screen capture, malwere execution, or spawning new Virtual opersing eystem environments.
- Also known as C & C or C^2
Execution
This can include extraction or destruction of IT and OT assets, installation of ransomware, IP theft, etc-
Cyber Kill Chain

Digital Forensics
Who - who are the attackers?
What - what did they take?
When - when did they get in?
Where - where did they go?
Why - why me? (why did my controls fail)
How - how did they get in?