12 - Email and Social Media Investigations
Class: CYBR-405
Notes:
Objectives
| Explain | Explain the role of e-mail in investigations |
|---|---|
| Describe | Describe client and server roles in e-mail |
| Describe | Describe tasks in investigating e-mail crimes and violations |
| Explain | Explain the use of e-mail server logs |
| Describe | Describe some specialized e-mail forensics tools |
| Explain | Explain how to apply digital forensics methods to investigating social media communications |
Notes:
- 97% of attacks come via email
- Over time computers have gotten so much more secure, yet has the volume of attacks reduce? No, every 3 seconds in the US there is a cyber attack
- This happens because we are humans, we like to touch stuff, break something and fix something else.
- Humans and passwords are the weak length in the chain
- Hackers don't break in they log in
- They are generally able to retrieve our passwords and use our credentials to start a session
Let's quickly talk about passwords
- Adversaries know we are creatures of habit
- We will use the same characters to represent the same thing
- Most people, because they have so many, will reuse their password
- Now the attacker can use the same password to log in to other places
- Length is the big indicator.
- Today NIST says 16+ character passwords are the way to go
- Long random alphanumerical characters that no-one could guess
- The Trusted Platform Model is a little hardware device embedded to your motherboard that specifically stores passwords and keys.
Password Attacks
Basic
- Brute Force
- Systematically try long lists of password combinations
- Look at Login Brute Forcing
- Dictionary Attack
- I can build a library of commonly used words and run an algorithm to use those words in combination to create possible passwords
- Pass-the-Hash\Rainbow Table
- For sale in the dark web
More Sophisticated
- Phishing
- Session Hijacking
- Kerberos Attack ("Kerberoasting")
| No. | Passwords | MD5 Hash | SHA1 Hash |
|---|---|---|---|
| 1 | 123456 | e10adc3949ba59abbe56e057f20f883e | 7c4a8d09ca3762af61e59520943dc26494f8941b |
| 2 | password | 5f4dcc3b5aa765d61d8327deb882cf99 | 5baa61e4c9b93f3f0682250b6cf8331b7ee68fd8 |
| 3 | 12345678 | 25d55ad283aa400af464c76d713c07ad | 7c222fb2927d828af22f592134e8932480637c0d |
| 4 | qwerty | d8578edf8458ce06fbc5bb76a58c5ca4 | b1b3773a05c0ed0176787a4f1574ff0075f7521e |
| 5 | 123456789 | 25f9e794323b453885f5181f1b624d0b | f7c3bc1d808e04732adf679965ccc34ca7ae3441 |
Hacking the mind is easier than hacking a computer
- Social Engineering is so much easier!
Notes:
- Today we have a man in the middle called Access Brokers, which get paid to gain access and sale those credentials on the dark web
- Access Brokers are very noisy and persistent: their mindset is low-level ethics - they are just doing a job
- But they can actually be arrested
Taking down a company
-
Company earnings about to be released
-
Learns about CEO
- via spouse on Facebook / social media
-
Contacts Sales via web
- gets email back with company signature
-
Creates a new URL just like company
-
Creates email to all C-Level directors
- "A letter from your CEO"
-
Uses signature from sales with CEO's name and info - crafted like the CEO would use (found out more using spouse)
-
Attaches PDF (mime only) with ransomware and exfiltration
-
Releases information to web - locks up company with ransomware
-
Shorted stock of the company - how much money?
Notes:
- People in business have to have this public persona, therefore it is easy to get some previous information about them
- Your sales department is just worried about doing the next sale so they will probably give you information.
- Nobody pays attention to the details:
- Make a fraudulent email close enough to the original that no-one would notice.
- 50% of ransomware attacks nowadays are double extortions. It may take the company two weeks to decrypt all the files. Once they decrypt all your system, they steal all your files, then they ask for a second ransom to not release these data to the public.
- This happens in a regular basis
Why is Social Engineering So Dangerous
- We are social creatures! We want to be helpful, therefore, you are more than capable of being easily fooled.
- Trust! There is no level of trust to avoid conflict.
- Information that you view as meaningless, we view as another piece to the puzzle.
- Look nice, dress nice and talk nice are valued techniques used to dupe you daily.
There are several methods social engineers use to get people to do things they wouldn't ordinarily do... pretexting
- Persuasion
- Impersonation
- Ingratiation
- Conformity
- Friendliness
Notes:
- We want to believe and trust that people are doing the right thing
- We believe in good rather than evil
- It is easy to bypass people thinking
- Note on campus we cannot just lock the doors, it is an academic environment, everything has to be open.
- IT people are famous for this - they want to help, they love being the saviors.
- He built the guys persona to get help from IT and make them visit a website for a project the persona was working on.
- Going to a website can be dangerous if it is compromised!
- Just visiting the website can deploy malware
Psychological Backdoor
We are all equipped with Psychological backdoors or triggers that are easily taken advantage of by social engineering.
Psychological Backdoor #1 - Because
Psychological Backdoor #2 - Liking
Psychological Backdoor #3 - Confidence
Psychological Backdoor #4 - Just Ask
Exploring the Role of E-mail in Investigations
An increase in e-mail scams and fraud attempts with phishing or spoofing
- Investigators need to know how to examine and interpret the unique content of e-mail messages
- Variation of Nigerian 419 e-mail scams
Phishing e-mails, text, or calls made with the intent to defraud.
- Spear Phishing - targeted at a specific individual
- Business Email Compromise - CEO Fraud
- Vishing
- SMSing
Pharming - DNS poisoning takes user to a fake site
- The phonebook to tell you here to go
- If you are able to poison that to tell google.com is your website, then you can hit people accessing google.com on that system
Business Email Compromise (BEC)
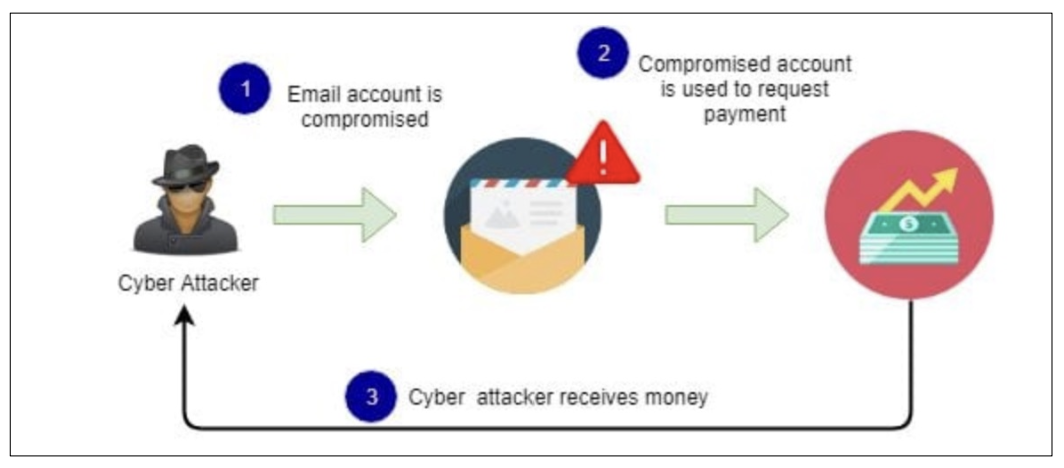
Sample BEC email
/CYBR-405/Visual%20Aids/image-5.png)
Actual Pharming Attack
/CYBR-405/Visual%20Aids/image-6.png)
Snail Mail
/CYBR-405/Visual%20Aids/image-7.png)
Notes:
- Each of these servers reads the email, and forwards it to the next email server
- We can either grab that email on the air or look at the byte stream being transmitted
Exploring the Roles of the Client and Server in E-mail
Name conventions
- Corporate: john.smith@somecompany.com
- Public: whatever@gmail.com
- Everything after @ belongs to the domain name
Tracing corporate e-mails is easier
- Because accounts use standard names the administrator establishes
Many companies are migrating their e-mail services to the cloud
Notes:
- As long as we have the
@and a direction, the email will know where to go
How does email know where to go?
Notes:
- We publish it out to let all the mail in the US to say that a message to that direction should be send to you
- This is done in an MX record, and it will take some time to propagate it to all the servers.
- Example:
- MX Record
___.yourdomain.compoints tomail.yourdomain.com
- A Record
mail.yourdomain.compoints to127.0.0.10
- MX Record
Investigating E-mail Crimes and Violations
Similar to other types of investigations
Goals
- Find who is behind the crime
- Collect the evidence
- Present your findings
- Build a case
Know the applicable privacy laws for your jurisdiction - Electronic Communications Privacy Act (ECPA) and the Stored Communications Act (SCA) apply to e-mail.z
E-mail crimes depend on the city, state, or country
- Example: spam may not be a crime in some states
- Always consult with an attorney
Examples of crimes involving e-mails - Narcotics trafficking
- Extortion
- Sexual harassment and stalking
- Fraud
- Child abductions and pornography
- Terrorism
Notes:
- Electronic Communication Privacy Act of 1986 (ECPA)?
- Prevents the government from being able to intercept these communication or wire tapping audio conversations.
- Each state sets their communication requirements
- If I have in a conversation and I am recording it, do you need to tell the other ones in the conversation? No, that is a one party setting
- Law enforcement needs a search warrant if the one party is not giving consent
- The law says that any email that is stored in that computer (a work computer) and I have consent to look at that computer, I do not need a search warrant to look at that email.
- Anything you say/do on a work computer is fair game as long as the owner of the device is the company, and the company allows it, this is at least here on the US.
Examining E-mail Messages
Access victim's computer or mobile device to recover the evidence
Using the victim's e-mail client
- Find and copy any potential evidence
- Access protected or encrypted material
- Print e-mails
Guide victim on the phone - Open and copy e-mail including headers
You may have to recover deleted e-mails
Copying an e-mail message
- Before you start an e-mail investigation
- You need to copy and print the e-mail involved in the crime or policy violation
- You might also want to forward the message as an attachment to another e-mail address
With many desktop e-mail programs, you can copy an email by dragging it to a storage medium - Or by saving it in a different location
Investigators should learn how to find e-mail headers
- GUI clients
- Web-based clients
After you open e-mail headers, copy and paste them into a text document - So that you can read them with a text editor
Become familiar with as many e-mail programs as possible - Often more than one e-mail program is installed
View headers in Outlook
- Double click to open as separate file
- Hit File button (top left)
- Hit Properties (bottom)
- Copy and Paste Header to a file for research
/CYBR-405/Visual%20Aids/image-8.png)
- Provides you with specific details from all the servers that the email passed through during transfer.
Headers contain useful information
- The main piece of information you're looking for is the originating e-mail's IP address
- Date and time the message was sent
- Filenames of any attachments
- Unique message number (if supplied)
- https://whatismyipaddress.com/trace-email
...
Intelligence Sources
- HUMINT - Human Intelligence
- SIGINT - Signals Intelligence
- IMINT - Image Intelligence
- TRASHINT? - digging through trash
- OSINT - Open Source Intelligence
What is OSINT
OSINT is defined as "intelligence produced by collecting, evaluating and analyzing publicly available information with the purpose of answering a specific intelligence question".
- Public Records
- News media
- Libraries
- Social media platforms
- Images, Videos
- Websites
- The Dark web
Notes:
- The first thing to evaluate on a company is what is publicly produced by that company
- Websites and social media, things of that nature
- Historically most organizations publish without thinking about security
- Most counties have their public records
The Dark Web
/CYBR-405/Visual%20Aids/image-9.png)
- Google only shows about 4% of the internet!
- Deep web are sites that are online accessible but provide some mechanism that stops unauthenticated people from seeing.
- Usually protected information like your bank account.
- Stuff that is online but is not publicly available
- Dark web is where you find a lot of the illicit activities
- Breaches
- We can monitor the dark web to look for breaches to our company, yes companies do this.
- Look at hacker forms and breach sites
- Is accessing the dark web legal?
- Yes it is completely legal
- Most people use the onion router (a TOR browser)
- Make sure you run some sort of EDR and a secure and anonymous connection so that you do not run into malware while visiting websites there!
- Background checks can sometimes look at your dark web activity, so be careful, though it is hard to track, they would have to have some very specific intelligence in order to do that
- There is a search warrant that says that anybody coming to a site is likely involved in illicit activity, and therefore inducts a warrant on all users visiting that dark web site
- If you visit that credential selling website, you will go to jail, you can have a malware installed and disclose your activity
robots.txttells indexers to not index this site!- Password protection is the biggest one of the reasons for not indexing
OSINT Data Sources
-
Social Media
-
Deep Web
-
Dark Web
-
Blogs
-
Digital Marketplaces
-
Maps
-
Libraries
-
Newspapers
-
Magazines
-
Public Records
-
Forums
-
Photos
-
Directories
-
Books
-
Radio
-
Data Leaks
-
Archives
-
Search Engines
-
Paste Sites
-
Chan Boards
-
"Normal Offenders"
- SnapChat
- TikTok
- Google Family-of-things
- Lesser Known
- Gab
- Parler
- MeWe
- Not Entirely Social Media
- Shopping sites
- Review Sites (Yelp, TripAdvisor, etc.)
-
General:
- Post/comment
- Reply
- Multimedia content (images and videos)
- Social interactions
- Metadata
Likes
In 2015, researchers from the University of Cambridge and Stanford University released a study illustrating how Facebook like data can be used to accurately predict a user's personality traits in a very powerful way. Back in 2007, researchers created an online personality test and posted it on Facebook. To take the test, users needed to give the researchers access to their Facebook data. The test went viral and over 80,000 people took the test and provided access. This meant researchers had not only the results of the personality tests, but also access to a vast amount of Facebook data.
The study eventually concluded that with just 10 likes, the algorithm would know you better than a work colleague. With 150 likes, it would know you better than members of your immediate family, and with just 300 likes, it would know you better than your spouse.
Notes:
- Google sells your data, and most companies do
- There has never been anything that is really impactful to prevent this, and it would be very difficult to ever find a solution to this, since they are such a big search engine
Types of Search Engines
All crawler based search engines use a crawler or bot or spider for crawling and indexing new content to the search database. There are four basic steps, every crawler based search engines follow before displaying any sites in the search results.
- Crawling
- Indexing
- Calculating Relevancy
- Retrieving the Result
Google Dorking
A term for leveraging specific "operators" in Google to find specific things faster or at all
- Google Dorking is often referred to as "Google Hacking"
- Built into a database: https://www.exploit-db.com/google-hacking-databa se
Some operators:
- site:
- inurl:
- intitle:
- filetype:
- allintext:
- date:
- author:
- cache:
- related:
- site: <site.domain> "(xxx) xxx-"
- site: <site.domain> "@site.domain"
- site: <site.domain> filetype:pdf
- site: <site.domain> filetype:.jpg
- site: <site.domain> robots.txt
Notes:
- Specificity is the name of the game.
- Google dorking makes search results more responsive to what we are looking for.
- If we engineer our prompt correctly, we can get more accurate search results
Username Enumeration
-
How many different social media sites do you all have access to?
-
Many sites have the user profiles visible to unauthenticated users
-
Others allow search engines to index their sites
-
Google Dorks for finding instances of usernames:
intext:<username>incache intext:<username>site:<website> intext:<username>
-
There are tools for performing username analysis:
- Sherlock
-
The WhatsMyName suite of tools and derivatives:
- Standalone WhatsMyName tool
- Recon-ng Profiler module
- WhatsMyName Web Application
- WMN_screenshooter
- nameFinder
Reverse Image Searching
Sites:
- Bing:
- Google:
- TinEye:
- Yandex:
Sherlock - usernames
/CYBR-405/Visual%20Aids/image-10.png)
Glo Avery case
| Platform | Usernames | Alias | URL | Notes |
|---|---|---|---|---|
| Telegram | gloavery | https://t.me/ | Glo's Candi Shop, suspected narcotics distributor profile | |
| Tik Tok | gloavery | https://www.tiktok.com/ | Subjects TikTok, Identifiable Videos with subjects confirmed location in College Station. | |
| glo.avery | https://www.instagram.com/ | Subjects private instagram account. Confirmed match | ||
| SnapChat | Classiccandi | https://www.snapchat.com/add/ | The subject has 2 identical SnapChat accounts with matching avatars, both private. | |
| SnapChat | gloavery | https://www.snapchat.com/add/ | ||
| candice.classic | Candice ClassicLethbridge | https://www.facebook.com/ | This account is suspected to be in relation to the subject (family member, probable mother). Note* the Subject and the women in this profile have extremely similar facial features. |
Notes:
- They were able to reverse ID her for her tattoos
- You do not need a warrant for OSINT
- It is all about what is my feeling on privacy