13 - eDiscovery
What is eDiscovery
eDiscovery (electronic discovery) refers to the process of identifying, collecting, reviewing, and producing electronically stored information (ESI) for use in legal cases. It is an essential part of litigation, regulatory investigations, and compliance processes, as much of the information relevant to legal matters is now stored digitally. eDiscovery helps attorneys and investigators find evidence in a range of electronic formats, such as emails, documents, social media content, instant messages, databases, and other digital records.
Overview of Rules, and Policies
- Digital data is often referred to as electronically stored information (ESI)
- This refers to any information that is created or stored electronically
- ESI can include data and metadata
- Data refers generally to information, such as documents, spreadsheets, graphics, and email, stored on digital devices
- Metadata refers to data about data
- In e-discovery, one party will ask the opposing party for data specifically related to the subject of the litigation
- Have a duty to preserve (prevent destruction) once you reasonably believe you will be a subject to litigation
- Request for Production (RFP)
- If you have it (and its relevant) you are required to produce it.
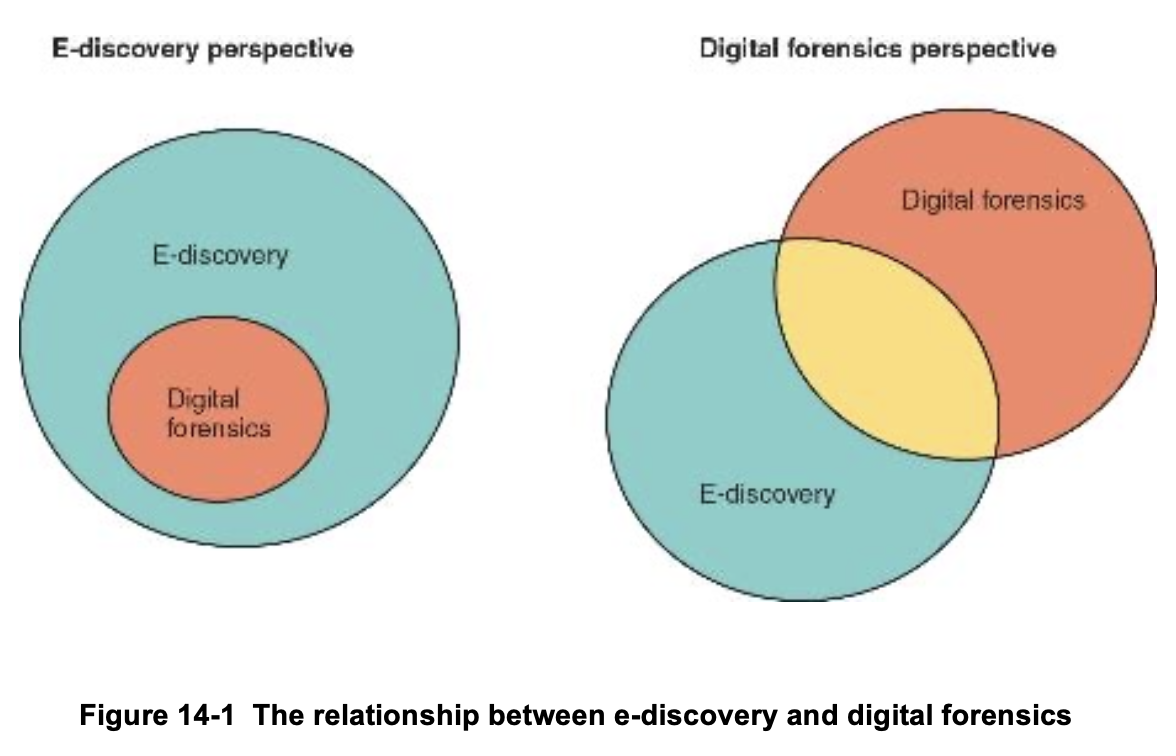
e-Discovery & Digital Forensics
- In digital forensics, the investigator is typically looking for information related to a criminal matter, corporate espionage, or a civil suit
- In e-discovery, the investigators know that they are looking for information related to a contract dispute, intellectual property rights, product defect, or false financial information
Notes:
- Only 10% of cases are eDiscovery
- This is changing with the number of breaches going out
Rules, Laws, and Regulations
- A wide range of rules, laws, and regulations influence e-discovery processes at the state and federal level
- Today, many companies have offices in different states and countries
- You must be aware of what laws are in effect when you are identifying and preserving data during e-discovery
- In the US, many employers require employees to acknowledge that the company has the right to monitor company email accounts
- This is not true in all countries, which can raise questions about what emails can and should be included in e-discovery
Federal Rules
-
The Federal Rules of Criminal Procedure (FRCrP) were established by the Supreme Court in 1944 and took effect in 1946
- They were intended to standardize the methods used for criminal proceedings in all states
- Rule 41 of the FRCrP addresses how evidence can be obtained in criminal investigations
-
Federal Rules of Evidence (FRE) went into effect in 1975 to ensure consistency in federal proceedings in both civil and criminal cases
-
The Federal Rules of Civil Procedure (FRCP) consist of 86 rules created in 1938 to provide "just, speedy and inexpensive" resolution of federal cases
- Rule 34 of the FRCP was introduced in 1970 to include ESI as part of discoverable material
- In 2006, the FRCP was updated to address additional issues related to ESI
-
Because of technology and case law changes, additional updates were made in 2016
Computer Fraud and Abuse Act
- The Computer Fraud and Abuse Act (CFAA) was passed to expand the scope of computer crimes covered by federal law to include those related to the unauthorized access of networks and computers
- It was passed in 1986
- The CFAA became important as hackers became more active
- e-Discovery is commonly used in CFAA cases
USA PATRIOT Act
- The USA PATRIOT Act was passed into law on October 26, 2001, as a result of the terrorist attacks on September 11, 2001
- Title II of this act expanded how digital evidence is collected and directly affects e-discovery
- It expanded what data could be seized and expanded wiretap laws
- Wiretaps could be used for a year, and they were allowed to follow the person, not the device
Notes:
- What does a terrorism law had to do with eDiscovery?
- The concept behind it was to clarify how digital evidence is collected and used in investigation, but it also refers to eDiscovery
- You now have the ability to wiretap as many devices as needed that follow the eDiscovery of a suspect.
- Our investigation is for an individual, not for a device
Sarbanes-Oxley Act
- The Sarbanes-Oxley Act (SOX) was passed in 2002 after accounting scandals at companies such as Enron and WorldCom left employees unemployed and without their pensions
- It addresses document and email retention
- The act created the Public Company Accounting Oversight Board (PCAOB), a nonprofit organization
- Monitor big accounting firms to check if they were truthful and doing what they are supposed to do
- The PCAOB has the following responsibilities:
- Register accounting firms that audit companies
- Perform inspections of registered accounting firms
- Establish standards for auditing, ethics, and quality control of same
- Investigate and discipline registered accounting firms for violations
- SOX was a good thing for us but created a lot of word for digital forensics investigators
- We need to make sure that what you are telling us is the correct information
Enron e-Discovery
-
Several factors led to the collapse of Enron Corporation including:
- Deregulation in the energy trading sector
- The use of mark-to-market accounting method, which is easier to manipulate and harder to track
-
These factors allowed top executives to hide the company's debt and ongoing losses
-
More than 20,000 people lost their jobs and Enron employees and retirees lost over $3 billion from their retirement and pension funds
-
The e-discovery process followed in the Enron case holds an example of what can go wrong
- PII included in many documents was not protected and made public
-
The database of Enron emails was available to the public for several years before it was sanitized and re-released
-
Many lawsuits resulted from the disclosure of the personal information
-
The lawsuits brought heightened awareness of some of the sensitive issues that must be considered as part of e-discovery
Notes:
- People were greedy, they will make a lot of money, and end up looking the other way
- Forensic examiners collected all the evidence, and made an investigation, there were requests from people to be able to look at this investigation material.
- They have all the HR and people SSN info
- It was the entire companies data
- Nobody had thought about public records holding personal information
- Anything seen by the court, after using it, becomes public information
The Sedona Principles
- The Sedona Principles provide recommendations for managing e-discovery
- They were published in 2007
- They are comprised of 14 principles that map to the Federal Rules of Civil Procedure (FRCP)
- They offer well-regarded guidelines and best practices for conducting e-Discovery
The Impact of Case Law
- Case Law is the body of law created by prior judicial decision regarding a particular legal issue is referred to as case law
- In a common-law system, evolving case law can establish a precedent that may alter existing laws and practices
- The United States and approximately
of the countries in the world use common law - In civil law nations, if a law specifically pertaining to the issues in dispute does not exist, the case cannot be tried
Case Law in the United States
- One example of the impact of case law in the United States is Olmstead v. United States
- In this case, which took place in 1924, law enforcement wiretapped Olmstead's phone without a warrant
- The U.S. Supreme Court ruled in that case that obtaining evidence through the use of wiretapping without a warrant did not violate the defendant's Constitutional rights
- The court held that the Fourth Amendment did not protect private telephone conversations, as they were akin to casual conversations overheard in a public place.
- The outcome upheld the use of warrantless wiretapping
- Another example of the impact of case law in the United States is Katz v. United States, which took place in 1967
- This case raised the question: was there an expectation of privacy and was the expectation reasonable?
- The Supreme Court ruled that Katz had a reasonable expectation of privacy when using an enclosed public phonebooth
- They determined that the FBI violated his Constitutional rights because they did not obtain a warrant before recording his calls
- This case overrode Olmstead and established a new precedent for interpreting the right to privacy under the Fourth Amendment
Notes:
- The FBI violated its civil rights because they didn't have a warrant
- When a case law gets decided and changes we make sure everybody is trained for that
- But after Katz, now you need to get a warrant to listen to a public conversation
EDRM
- The Electronic Discovery Reference Model (EDRM) is a conceptual framework created to address how to process ESI in a legal case or investigation
- The current model is shown on the following slide
- It was created specifically for e-discovery and a large international group maintains the model
- It was developed to ensure ESI makes its way to court in both civil and criminal cases
/CYBR-405/Visual%20Aids/image-11.png)
Notes:
- It is a plan for how do we do eDiscovery
- It is a framework
- Look at Figure 14-11 Electronic Discovery Reference Model (EDRM)
- Once I have identified all the data, we move on to the collection stage
- Wayback machine is allowed in courts, it records URL and data at the time of the issue
- Extremely useful tool for looking at historical websites
- In about every case of eDiscovery, we over-collect, because we never go in what direction the investigation would move
- Remember data also changes over time
- If you over-collect, you freeze this data at that time
Stages of the EDRM
-
The EDRM has the following eight stages:
- Identification
- We need to know what we need to look for and where data is stored
- Preservation
- When we collect data we do it in such a manner that we preserve it
- Collection
- We make two copies, what we will work with, and the original untouched data
- Processing
- Building a nice hierarchical chain that shows where the data is coming from, removes duplicates and puts everything in readable format
- Review
- Done by attorney
- Analysis
- Ask questions about the data, is something missing?
- Production
- Produce (ready for to the court)
- Presentation
- Present it to the court
- Identification
-
Identification and preservation may begin before a legal case has started
- When an organization is notified it may be involved in a lawsuit, it's legal team should issue a litigation hold
- A litigation hold informs employees that they must stop overwriting backups, deleting files, and performing other tasks that could destroy evidence related to an anticipated litigation
- Failure to preserve data is called spoilation and can result in sanctions
-
Information gathered during the collection stage must be readily accessible as well as legally defensible, meaning it will stand up to a challenge in court
Maziar v City Atlanta
Text Message Spoliation Leads to 37(e)(1) Sanctions: eDiscovery Case Law
Retaliatory Termination
- LitHold sent November 4, 2020
- Maziar fired 6 months later
- City finally issues a hold order
- Did not include phones (any/all)
- When RFP sent - supervisor quit &
- Wiped her work and personal phone
Notes:
- The reason it needs to include any and all, is because it needs to preserve any and all data that relates to this case (any and all sources)
- The moment the attorney sends the request for production the supervisor quits
- Once doing forensics they found a fragment of a text message
- The plaintiff thus sought sanctions based on defendant's text message spoliation and failure to produce responsive text messages specifically regarding the remainder of the cropped message and any relevant texts preceding or following it. The magistrate judge denied the motion and the plaintiff filed objections.
What about personal devices?
-
Does any and all includes personal devices?
- Are they involved in eDiscovery?
- It depends, do people use their personal devices and personal email for work stuff
-
Long Island, Inc v. Town of Oyster Bay
- Personal devices used for business
- Rule 34(a)(1) permits requests for "documents and ESI within the party's possession, custody, or control"
- They were able to show that there were some business text messages on personal devices
- 9/10 people, they will fight for not showing their personal device
- Once "control" has been established, a requesting party ...
What about data inside a database?
- Sound Around, Inc, v. Moises Friedman, 24-CV-1986
- Defendants counterclaimed for the value of certain commissions they claimed to be owed by Plaintiff.
- Group of employers get sued by the previous employer saying "you should have done that".
- There was some data to support this claim
- Its in the database, if its in the database we can search it easily
- The information in the database actually proved that the employees were telling the truth
- Sometimes the sanction you get by the court can be higher than the litigation
- Court can also decide to not sanction the entire company but the attorney
- Skanska USA Civil Southeast, Inc. v. BagelHeads, Inc., 75 F.4th 1290 (11h Cir. 2023)
- The company gained a sanction because they did not accomplish obligations of backing up their data, they should have had it, but because they didn't they are now liable.
- This happens way too frequently
- The computer was ran over by a vehicle
- My cell phone fried!
- Wegman v. United States Specialty Sports Ass'n, Inc.
- Former employer did not present evidence, they did not return computers, cell phones to us
- There is some information that the only place where it leaves is on a single device
- Plaintiff's retention of the company's 3 electronic devices prevented the organization from ...
Is a text message by itself enough?
-
Can you alter a text message?
- Yes
-
Can you alter an email or any kind of electronic communication?
- Yes
-
There needs to be some way to verify the integrity of a message
-
Walker v. Harley-Anderson, 301 So. 3d 299, 302
- They were going to arrest her because somebody made an allegation that she had illicit content on her facebook account
- Electronic evidence can be altered, fabricated, changed!
- "Testimony is not enough!"
Can you use AI in the court?
- Mata v. Avianca, Inc., 22-CV-1461 (PKC), 2023 WL 4114965
- Attorney uses ChatGPT to generate fake information
- Fake identities, fake streets and locations, etc.
- ChatGPT created filings that included "non-existent judicial opinions with fake quotes and citations", and failed to admit this usage when questioned by the court.
- But the worst thing is that the attorney lied ("failed to admit" = lied)
- He must had been asked where did he got that info from.
- AI is getting better, but still makes hallucinations today
- We just need to tell the truth
- Courts now mandate that if the attorney uses AI, that they need to disclose it in the file
- Attorney uses ChatGPT to generate fake information
Stages of the EDRM (2)
-
During the processing, review, and analysis stage, redaction and deduplication work occurs
- Deduplication reduces the amount of data included as part of e-discovery by identifying and removing duplicate documents, emails, and other types of data
-
After data has been retrieved, the files need to be scanned for viruses
-
Documents that include content that is covered by attorney-client privilege or is an attorney work product must be removed unless the client grants permission to include them
- A log of withheld documents must be kept
-
The review and analysis processes continue as the team moves into the production phase, which involves generating the ESI in the manner agreed upon
-
The final phase of the EDRM model is the presentation phase
- Presentation may occur at a deposition or hearing, during mediation, or at a trial with a judge and jury present
Common e-Discovery Tools
- e-Discovery software can be quite expensive for the enterprise level
- Forensics software can be used in some e-discovery cases
- The desired outcomes are not always the same
- Digital forensics software acquires the data, searches for deleted data, validates data using hash values, and preserves evidence
- e-Discovery software typically does not look for deleted files
Summary
Now that the lesson has ended, you should be able to:
- Describe e-discovery and its relationship to digital forensics
- Explain the impact of case law on e-discovery
- Outline the phases of Electronic Discovery Reference Model and the ediscovery case flow